Chinese spy cameras remain in widespread use in the United States, in Canada and Mexico and worldwide. They are sold as security and traffic cameras, but that is a cover story for their real use. Such cameras are used for social and political control turning countries into digital prisons.
The US and Israel have been able to hack them. In places where they are banned, China is now using drones to conduct spying in place of fixed installation cameras.
The recent persistent Barksdale Air Base drone incursion along with many others may be China’s partial answer to the ban on its security cameras. In fact, the rise of drone security incidents corresponds almost exactly to the US 2019 ban on Chinese cameras at American military bases.
What is happening in the United States is taking place elsewhere.

Back in 2018 I discovered a sole source contract for Hikvision cameras for the US Embassy in Kabul, Afghanistan. Hikvision is Hangzhou Hikvision Digital Technology Co., Ltd. It is a publicly traded company, but it is effectively controlled by the Chinese government. While it is listed on the Shenzhen Stock Exchange (SZSE: 002415), its ownership structure is a mix of state-owned enterprises (SOEs), private founders, and institutional investors where state-owned enterprises control more than half the company.
Why, I wondered, was the US Embassy in Kabul ordering Chinese cameras for its security, and why was the contract sole-source, meaning no other camera would qualify for the job? As I began asking questions about the announced contract (a sole source announcement means the deal is done), I found out that Hikvision, along with another Chinese camera company, Dahua Technology (Zhejiang Dahua Technology Co., Ltd.), apparently had weak security amounting to a functional back door. These cameras work through the Internet and can be easily hacked.

The problem, it turned out, was far bigger than the Kabul embassy. Chinese cameras made by Hikvision and Dahua were being used throughout the US government for security, including at military bases.
Since 2003 China has put in place what it calls a Safe City (Ping’an Chengshi) program. This program is the framework for China’s massive internal surveillance system, which uses cameras, facial recognition, license plate readers, and artificial intelligence for social and political control and security protection.
China has exported this system to many African countries including Kenya, Uganda, Ethiopia, Egypt, South Africa; in South East and Central Asia including Pakistan, Laos and Myanmar, Uzbekistan and the Philippines; and in Latin American countries including Brazil and Venezuela. In the Middle East, Safe City has been implemented in the UAE and Saudi Arabia, and also Iran.

Any security system that has a backdoor or is otherwise connected to the Internet can be hacked. This is exactly what happened recently in Venezuela and Iran, except Venezuela’s extensive cameras and surveillance system was hacked by the United States, and Israel hacked Iran’s system that protected regime leaders, turning the tables on these regimes and on their Chinese provider.
In Venezuela in the run-up to the capture of Venezuelan President Nicholas Maduro, the US exploited the vast network of Hikvision and Dahua cameras installed throughout Caracas.
The Wall Street Journal reported that the US Cyber Command utilized “pre-positioned malware” in critical systems. This allowed Cyber Command to create “shadow administrators” within the camera networks to watch Maduro in real-time while hiding the US presence from the guards’ monitors.
During a press conference at Mar-a-Lago on January 3, 2026, General Dan Caine, chairman of the Joint Chiefs of Staff, detailed the extreme level of surveillance the US military and intelligence agencies maintained on Maduro in the months leading up to Operation Absolute Resolve.
The intelligence community worked to find Maduro and understand how he moved, where he lived, where he traveled, what he ate, and what he wore, and even identified his pets.
What the US did in Venezuela the US and Israel did in Iran, which led to the death on February 28, 2026, of Iran’s Supreme Leader Ali Khamenei along with other top Iranian leaders.
Israeli intelligence reportedly gained access to Tehran’s vast network of urban surveillance cameras years before the strike. By hacking cameras in parking lots, residential streets, and shift-change points, analysts used AI to map the “rhythms” of bodyguards and drivers, as it was easier to follow bodyguards and drivers than to follow Khamenei and other officials.
A specific camera near the leadership compound on Pasteur Street allowed analysts to observe exactly which vehicles were entering and leaving, and at what times, providing a real-time “trigger” for the strike.
Hikvision and Dahua are the most widely deployed cameras in Iranian cities. Iran sought to build a “digital iron curtain” using Chinese hardware for this purpose. Another Chinese company, Tiandy, provided high-end cameras with low-light “Starlight” technology and facial recognition to Iran’s Revolutionary Guards (IRGC).
Hikvision alleged arrests
Jennifer Zhang on X reported on April 8 that China had arrested 300 Hikvision employees, allegedly for espionage.
Her report, she said, is based on the work of the respected Chinese-Canadian journalist and dissident Sheng Xue. As a correspondent for Radio Free Asia and Deutsche Welle, Sheng Xue has frequently discussed the “digital iron curtain.” Many of her articles are published in Chinese.
Shen Xue’s commentary often focuses on the use of AI and facial recognition (Hikvision’s core business) to track dissidents abroad. She has also commented on the “Safe City” initiatives that export Chinese surveillance models to other nations. Sheng Xue also continues to complain that Canada permits Hikvision and other Chinese cameras to be used in Canada, by Canada’s government and military among others.

There were widespread reports in late 2024 and early 2025 concerning mass layoffs and “adjustments” at Hikvision, apparently triggered by financial problems. How these reports relate to the latest information is not clear. For example was there an actual political purge in 2024 and 2025, or is there one now with the alleged arrests?
It is quite true there is genuine alarm inside China over the performance of Chinese defense technology in Venezuela and Iran. Noteworthy are failures of Chinese-supplied air defenses and radars. Whether this extends to the vulnerability of Chinese-supplied surveillance networks is not known, but it makes sense given that knowledge of the compromise of these Chinese-supplied systems is now public.
The US problem
Many countries continue to use Chinese surveillance technology even though the technology is highly vulnerable to hacking. This includes the United States. While the US government is trying to remove Hikvision, Dahua and other suspected “white label” cameras and systems in government and military installations, commercial enterprises and non-government organizations, as well as property owners and operators, can still purchase previously imported models. However, as of April 4, the Federal Communications Commission (FCC) proposed an expansion of its existing rules that would move from a “new model ban” to a complete import ban.
Following the National Defense Authorization Act (NDAA) of 2019, the Department of Defense (DoD) was mandated to remove all video surveillance equipment manufactured by Hikvision and Dahua (and their subsidiaries) from federal facilities. Before the ban, these cameras were ubiquitous on US bases.
Even so there is still a problem with “white label” products and Chinese chipsets and Chinese firmware showing up in domestic products. The most persistent issue in 2026 is not the brand on the box, but the System on a Chip (SoC) inside. Under Section 889 of the NDAA, a camera is non-compliant if it contains “substantial or essential” components from the banned entities.
Cellphones and drones as camera-spy replacements
If a drone flies over an air base it can identify cellular phones on the base and “read” the radio transmissions of other equipment including tactical radios, radars and other command and control assets. By identifying mobile phones, hackers can go to work planting spyware on them.
While officials are not supposed to use mobile phones for classified work, they may keep much unclassified information on them, including names of colleagues, email and phone numbers, home addresses, travel information and financial data. Because phones today are loaded with images, the faces of top officers and technicians and pilots (on air bases) can be used for identification and tracking. Once a phone and user is identified, the phone’s whereabouts can be tracked.
Much depends on the sensors on the drone and how the drone communicates. Today even low cost drones can be linked to satellites. Before Elon Musk started to geofence the Russians, Russia was putting Starlink on its drones and using them over Ukraine. But domestic users are not limited or geofenced. Starlink can support 4K level video and high speed data transfers.
The number of drone-linked events over military bases, government installations, and significant industrial and infrastructure elements suggests that China or other adversaries may have turned to using drones instead of fixed cameras for sophisticated spy operations. From November to December 2024, thousands of witnesses reported drones over multiple states. While many were FAA-authorized, the Pentagon confirmed hundreds of concurrent unauthorized incursions over sensitive defense sites during this window.
Just weeks ago, unidentified drones were spotted over Fort McNair in Washington, D.C., triggering high-level White House meetings and elevated force protection levels. Secretary of War Pete Hegseth and Secretary of State Marco Rubio have residences on the base.

The persistent drone event over Barksdale Air Force Base in March, 2026, during the loading of B-52s for Operation Epic Fury, suggests an attempt to surveil and perhaps delay launches of B-52s headed to Iran.
There are many more. Langley Air Force Base in December, 2023 involved drone flights over 17 consecutive nights. A swarm of up to 15 drones (some the size of a small car) flew over the flight line.
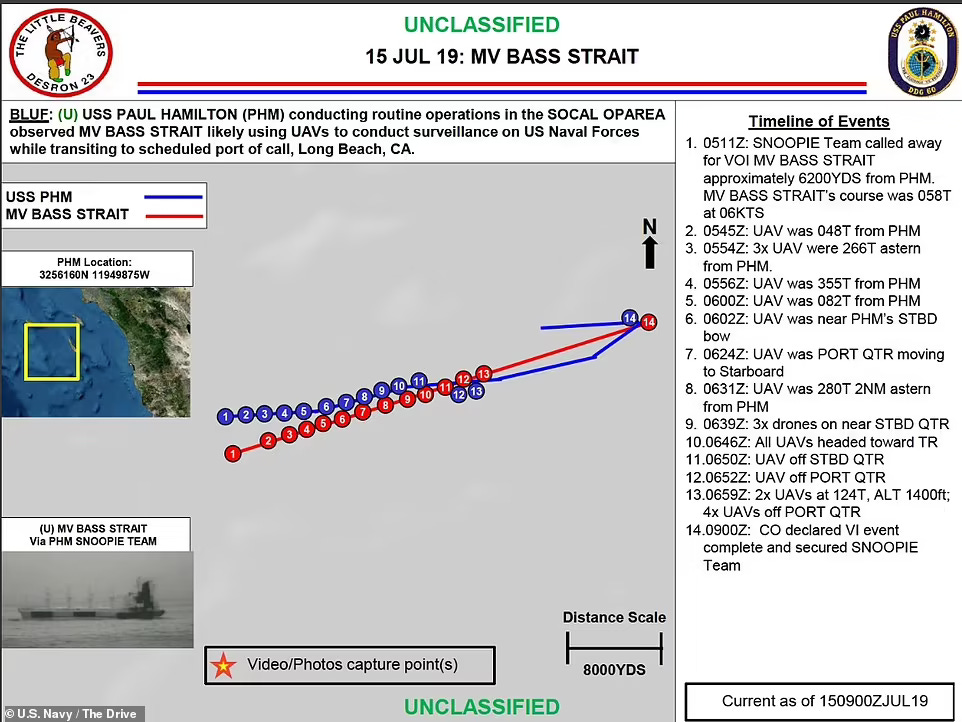
Off the coast of Southern California (near Los Angeles), a fleet of US Navy warships in 2019 was shadowed by dozens of drones for several weeks. Initially investigated as UAPs, they were later linked to a Hong Kong-flagged freighter, the MV Bass Strait.
It is noteworthy that there have been more and more threatening drone events since the US government banned Hikvision, Dahua and other Chinese cameras.
Ironically the ban on Chinese cameras has generated a dangerous replacement, the sophisticated surveillance drone. Drones can be launched from nearby countries or from ships. They can be brought into the United States and operated by drone teams that have crossed our borders. We are just at the beginning of the drone war here at home. The Pentagon has not come up with a strategy to stop the incursion.
Stephen Bryen is a former US deputy under secretary of defense. This article first appeared on his Substack newsletter Weapons and Strategy.








