Southeast Asia is watching the US-Israel conflict with Iran — and quietly drawing conclusions. Most countries have adopted a policy of non-interference, but behind the cautious and neutral stances, they are accelerating efforts to reduce their defense dependence on Washington.
The recent US-Indonesia defense agreement, followed by an apparent rift between the Indonesian defense and foreign ministries over granting the US overflight rights above the Strait of Malacca, resulting in a hold on access, clearly illustrates this tension.
President Trump’s unpredictable, transactional foreign policy has widened the divide between Washington and many Southeast Asian capitals. Eroding trust and diminishing alignment are increasingly visible, while US disengagement from Association of Southeast Asian Nations (ASEAN) multilateralism signals a diminishing role in the region.
Though suggestions of a diminished US role in the region have circulated for some time, they have not always been backed by concrete evidence or outcomes. Successive administrations managed to reassert engagement after periods of drift. Those were seen in the “Pivot to Asia” under Barack Obama, the Indo-Pacific strategy during the first Trump administration and its continuation under Joe Biden.
At present, however, US influence appears to be declining more markedly. One key and visible indicator is the absence of unequivocal support from allies and partners during the ongoing Middle East crisis. Even traditionally friendly countries have voiced criticism of the US’s war against Iran.
For instance, Singapore Foreign Minister Vivian Balakrishnan stated in late March: “I was surprised by the onset of hostilities. I did not think it was necessary. I do not think it is helpful. Even now, there are doubts about legality. For 80 years, the US underwrote a system of globalization based on UN Charter principles, multilateralism, territorial integrity, and sovereign equality. It led to an unprecedented period of global prosperity and peace.”
Another important indicator is the ISEAS-Yusof Ishak Institute’s State of Southeast Asia 2026 survey. Unsurprisingly, regional attitudes toward China and the US have shifted in recent years.
According to the survey, 52% of respondents now favor alignment with China, compared to 48% who still prefer the US. While the overall margin is narrow, the finding is nonetheless noteworthy: China is now perceived as more closely aligned with the interests of ASEAN member states than the US.
More striking, however, are the variations across individual countries. In Indonesia (80%), Malaysia (68%) and Singapore (66%), respondents show a clear preference for alignment with China over the US. By contrast, only 23% of Filipino respondents express a similar inclination toward China.
Two major factors underpin this shift. Most immediately, the conflict and disruption of the Strait of Hormuz have severely impacted ASEAN economies.
The ASEAN Centre for Energy reported that Middle Eastern crude made up 56% of ASEAN’s total crude imports last year. The resulting energy shock is the most visible consequence, with effects already felt across regional markets. Foreign investors, for example, are selling Thai assets amid concerns about energy price volatility stemming from the US-Iran conflict.
Second, rapidly declining confidence in the US is a critical factor. Perceptions of unpredictability — from the imposition of tariffs to a lack of sustained economic and security focus on the Indo-Pacific — have reinforced doubts about Washington’s reliability.
Trump’s transactional, temperamental and often flippant approach to foreign policy has prompted a serious recalibration among allies and partners in the region.
With US attention and resources overstretched across multiple conflicts from Europe to the Middle East, and a focus on America First at home and abroad, such a regional recalibration is both justified and understandable.
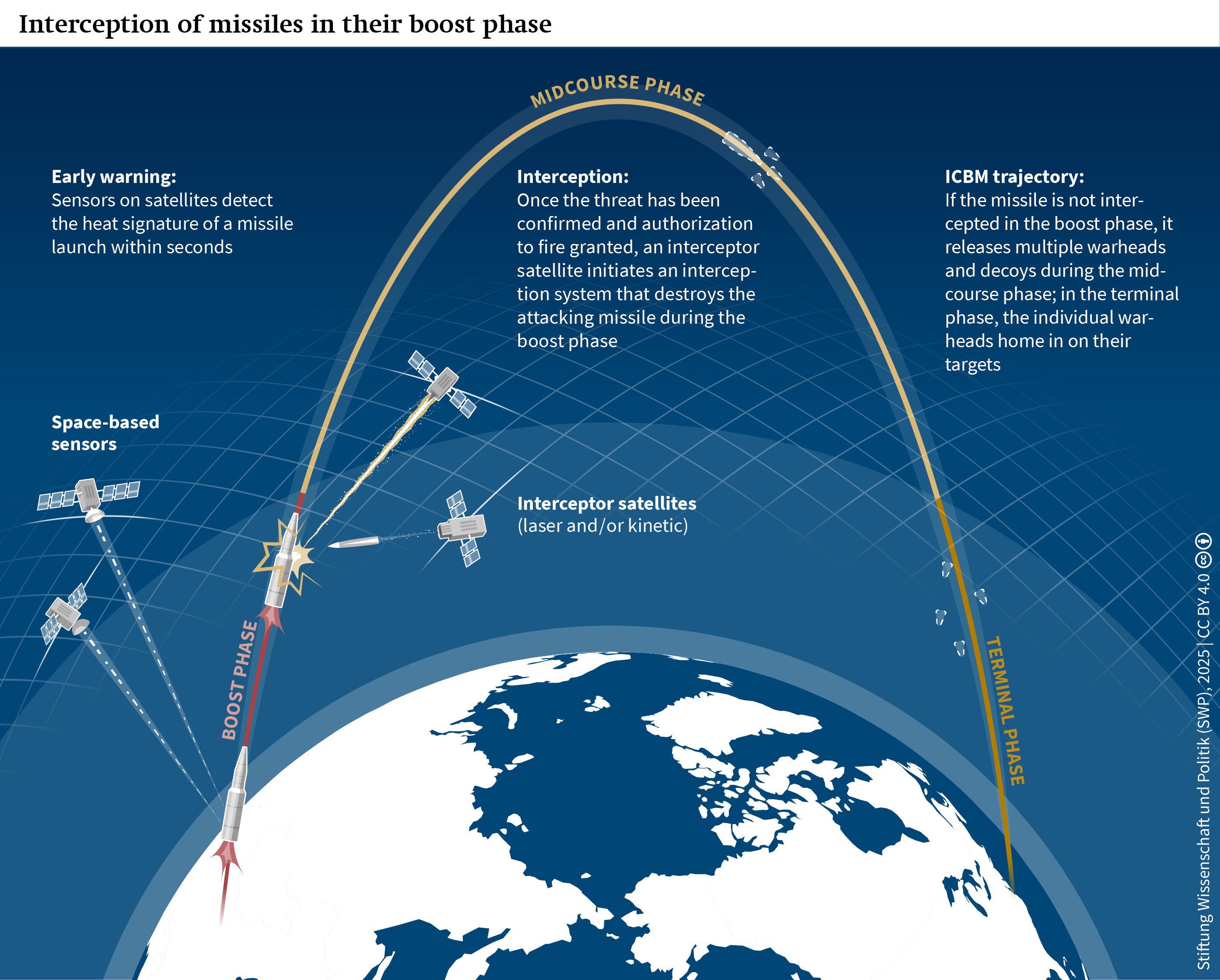
The apparent US failure to shield its partners in the Gulf from Iranian attacks is a grim reminder that self-reliance, complemented by credible strategic support from major powers, remains the ultimate guarantor of security.
For many middle and small regional powers, the choice is no longer limited to the US or China. While trust in Washington is clearly in decline, it does not automatically translate into alignment with Beijing.
Instead, most Southeast Asian countries are prioritizing flexibility and diversifying their strategic partnerships. Japan, Australia, India, Turkey, the United Kingdom and the EU are seen as partners with untapped potential.
The US-China dynamic is often framed as benefiting China, but that view is overly simplistic. Divisions within ASEAN persist, especially regarding the South China Sea.
While China has frequently exploited differences among ASEAN members, this fragmentation also creates challenges for Beijing. The Philippines’ more assertive stance, for example, has complicated China’s efforts to maintain a consistent regional strategy.
The US-Israel-Iran conflict has made clear that ASEAN member states do not view it as their conflict, prompting a reassessment of their global positions and creating space for more autonomous foreign policies.
Crises can present opportunities. For many ASEAN states, this may be the moment to address internal divisions and pursue a more coherent, collective approach — one that strengthens the bloc and reduces vulnerability to external shocks.
Dr. Rahul Mishra is an associate professor at the Centre for Indo-Pacific Studies, School of International Studies, Jawaharlal Nehru University, New Delhi, India, and a senior research fellow at the German-Southeast Asian Center of Excellence for Public Policy and Good Governance, Thammasat University, Thailand. He is also the series editor for the Palgrave Series in Indo-Pacific Studies. He can be reached at rahul.seas@gmail.com and tweets at @rahulmishr_